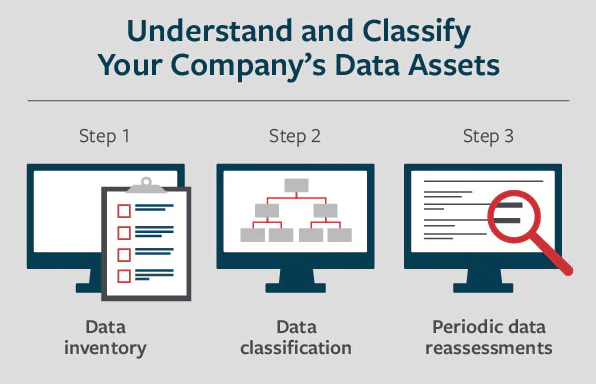
3 Steps for Data Assessment, Inventory & Classification
Know Your Data and How to Protect It.
Because businesses and organizations collect many different types of information, to help quantify their cyber security risk exposures, companies should first understand the types of information they are collecting, storing and sharing. This information can range in complexity from a simple inventory of products to personal information, including private health and financial records. Personal and customer information may be subject to federal, state and local regulations, Payment Card Industry standards, or perhaps foreign privacy standards.
While having a data security policy is the first step to help protect your data, the next logical step is to inventory all the data you handle during the course of business. This can help you classify it based on its confidentiality to determine who should be authorized to access it and to determine the level of data security needed.
What Kind of Data are You Handling?
Here is a three-step process that can help companies understand and classify their various data assets.
Step 1: Data Inventory
Determine the type of data you store.
- Personally Identifiable Information: Often referred to as PII, this information may include such things as first and last names, home or business addresses, email addresses, credit card and bank account numbers, taxpayer identification numbers, medical records and Social Security numbers. It also may include gender, age, date of birth, city of birth or residence, driver’s license number, and phone numbers.
- Customer information: This may include payment information such as payment card numbers and verification codes, billing and shipping addresses, email addresses, phone numbers, and purchasing history, among other data.
- Intellectual property: This may include proprietary and sensitive business information such as financial records, product designs, human resource records and internal correspondence and reports. It also can include intellectual property of others with whom you have a business relationship, including customers and vendors. Read More